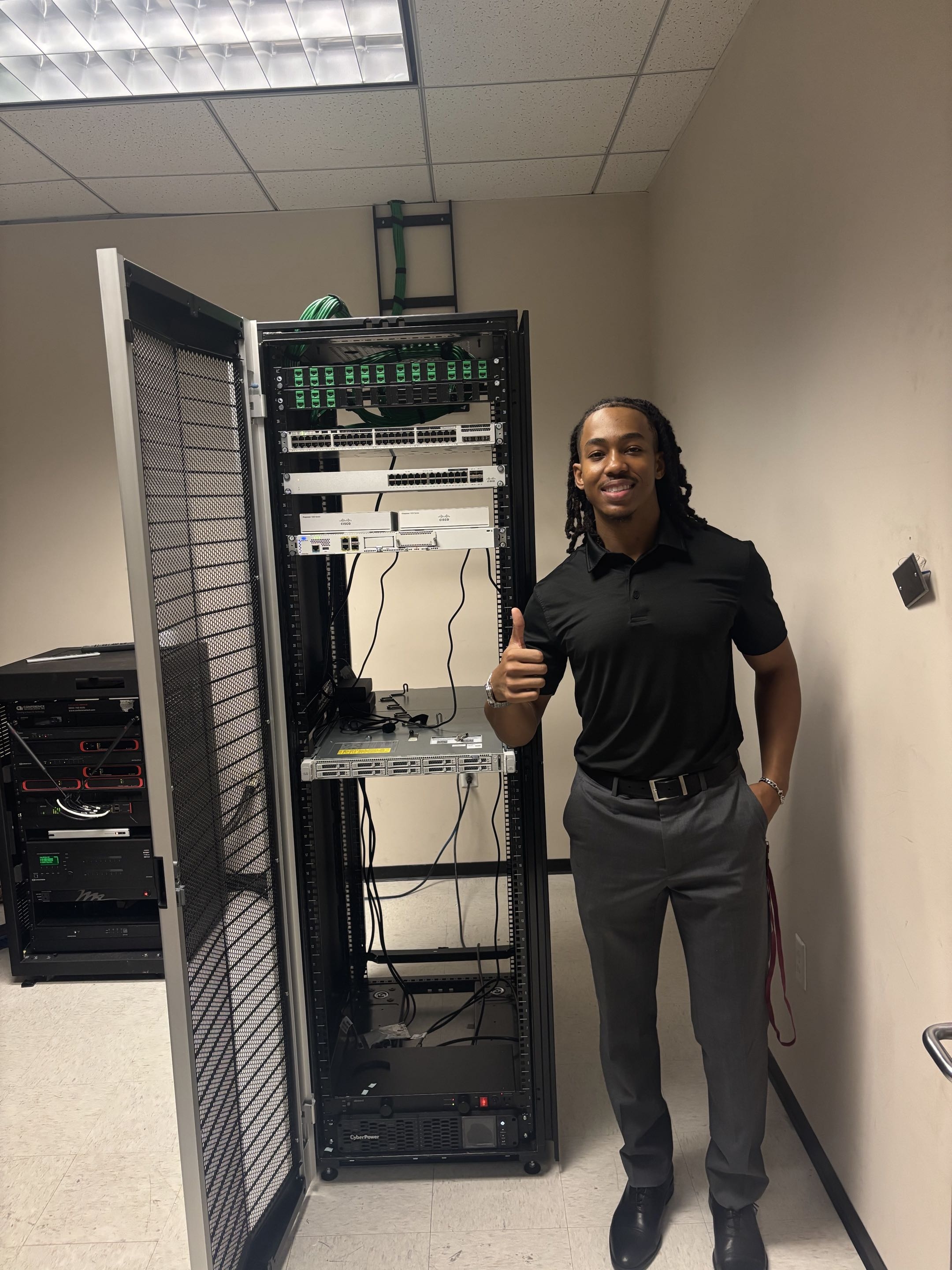
Cybersecurity Infrastructure Support Technician
Texas Southern University
Apr 2025 - Present
- Lead student technician for TSU's first dedicated cybersecurity teaching lab
- Configure and maintain Cisco Catalyst 9200/8200 core switching, Meraki MS130, and Firepower 1000
- Design VLAN architecture isolating student, management, and production traffic